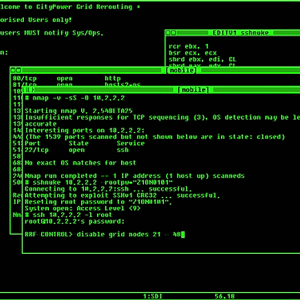
Just in case there’s a few designers out there who still haven’t gotten the word, here’s a great, simple explanation of how web page code injection works. It’s astonishingly simple. Read through this example, then try it on your own website if you have a PHP page that takes variables as part of its URL (who doesn’t these days?). In a nutshell, code injection works when your URL ends with something like “?search=something” and then your script does not check for valid input in the variable “search” before using it.
 XSS vulnerabilities are also easy to discover. For instance, imagine a cURL script that runs through your bookmark file and looks for the characters ‘?’ or ‘=’ in a link. It then tries to fetch a page for each of those links with something like ‘
XSS vulnerabilities are also easy to discover. For instance, imagine a cURL script that runs through your bookmark file and looks for the characters ‘?’ or ‘=’ in a link. It then tries to fetch a page for each of those links with something like ‘
‘ and then checks the returned page for the text ‘EXPLOIT ME’ somewhere in the body. If it finds that, it adds the link to its list of pages with exploit potential.
You could just Google random dictionary words and find dozens of sites per day with a system like that! So don’t assume that a potential vulnerability will never be found – they get discovered and used every day. (more…)


 Briefly, credit card
Briefly, credit card